We’ve heard a lot about cyberattacks lately, with news about incidents travelling far, wide and fast. That’s hardly remarkable, given that attacks can cause highly sensitive information to become public, personal information can be stolen and entire companies can be shut down whilst cybercriminals wait for a ransom to be paid. In short, the economic and social impact is high. Recently, NotPetya dominated the news with both the Maersk terminal in the Port of Rotterdam and TNT post being hit. Using both online and offline media monitoring we found that there were more than six thousands articles and posts about the virus in just the first few days of the attack.
The media covered, among other things, the cause, the victims (and the associated economic damage), 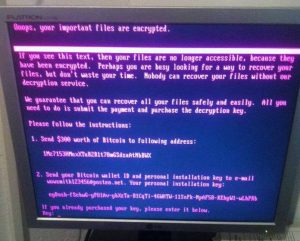 the modest amount of money the hackers demanded and the peculiarities of the attack. Also noticeable was the fact that many security experts and security companies jumped on the news. For example, we saw comments from spokespersons from Kaspersky, Fox-IT, DearBytes, ESET and Comae. Kaspersky dominated the news with around 180 articles. The national newspaper De Telegraaf took a different approach and investigated the legal implications of the breach by talking to internet lawyer Christiaan Alberdingk Thijm at Bureau Brandeis. He pointed out these attacks are a trend and urged companies to take measures as quickly as possible to improve their digital security. This is especially critical given that, next year, the new General Data Protection Regulation will take effect.
the modest amount of money the hackers demanded and the peculiarities of the attack. Also noticeable was the fact that many security experts and security companies jumped on the news. For example, we saw comments from spokespersons from Kaspersky, Fox-IT, DearBytes, ESET and Comae. Kaspersky dominated the news with around 180 articles. The national newspaper De Telegraaf took a different approach and investigated the legal implications of the breach by talking to internet lawyer Christiaan Alberdingk Thijm at Bureau Brandeis. He pointed out these attacks are a trend and urged companies to take measures as quickly as possible to improve their digital security. This is especially critical given that, next year, the new General Data Protection Regulation will take effect.
A survey of the Dutch national and tech news Progress Communications recently conducted, shows that newsjacking is very popular. That also applied to the NotPetya attack, with many journalists saying that after the attack they very quickly received editorial contributions from security providers. These companies offered blogs, press releases, or made experts available for interview. Sometimes these contributions were published, but most journalists indicated that they already had a wide range of contacts themselves and preferred to approach them for comment. Some sought collaboration with other media to publish as quickly and fully as possible.
What do these results mean for PR managers?
What these outcomes show is that you generally have to offer an in-depth response with newsjacking. Journalists are looking for additional news coverage. They also want to report what is happening behind the news. So, keep that in mind and make sure you offer added value.
Also, make sure you provide a technical and well-substantiated advice or comment as it’s very painful if you obviously want to share, but lack the expertise needed to share something of value. In that case it’s better to keep quiet, according to the media surveyed. It’s also certainly not a good idea to promote yourself in your comments. This may be obvious, but make sure your message is not attributed to or centered on the products or services your company offers as journalists can spot this from a mile away. With objective and practical comments, you can create awareness and the media will acknowledge that you can meaningfully contribute to the wider security conversation.
Keep it clear
In addition, it is important to offer a clear and concise message that needs little work to be published on paper or on a website. It is also useful to keep in mind to focus on the impact of an attack for the general reader as the public may be less interested in what companies have done wrong or should do in the future.
Speed
Speed is critical. The media want to publish news and commentary as soon as possible. That’s one of the reasons why they often turn to their regular database filled with people they know and trust.
Do you need help with your media approach? Let us help you. Our day begins with the scanning of the newspapers, the main news sites, and other press outlets. In addition, we use a variety of on and offline monitoring tools. Thus, we know exactly what it is going on and how we can respond.
